Why Full-Stack Post-Quantum Cryptography Cannot Wait
April 01, 2026 -- As large enterprises modernize their networks for the AI era, one challenge stands out: the looming risk posed by quantum computing. At Cisco Live 2026 Amsterdam, Cisco responded by introducing what we describe as the industry’s first full-stack post-quantum cryptography (PQC) architecture.
This solution applies quantum-safe cryptography across every layer—from device integrity at boot to data in transit protection for critical connections—using National Institute of Standards and Technology (NIST)-approved quantum-resistant algorithms. For network engineers and security architects, this marks the most significant cryptographic leap in more than two decades.
Understanding the cryptographic challenge
PQC addresses a structural weakness exposed by quantum computing in modern cryptography. While strong symmetric encryption such as Advanced Encryption Standard-Galois/Counter Mode (AES‑GCM) may already be in place to protect data, the cryptographic mechanisms used to establish and exchange those encryption keys are expected to become vulnerable to quantum-based attacks.
For large-scale organizations running vast, multisite networks, this vulnerability represents not just a technical concern but a business continuity risk. Algorithms such as Rivest–Shamir–Adleman (RSA) and Elliptic Curve Cryptography (ECC) remain secure against classical computing but will not withstand cryptographically relevant quantum computers—systems powerful enough to break today’s widely deployed public-key cryptography.
The growing threat of harvest now, decrypt later
This weakness is what makes the harvest now, decrypt later (HNDL) threat so serious. Sensitive encrypted data is already being collected at scale across enterprise networks and digital services. While this data remains protected today, it is being retained by attackers with the expectation that quantum computers will expose it. When a cryptographically relevant quantum computer emerges, years of accumulated data could be exposed at once, creating a long-term risk for organizations that do not act now.
The expanding scope of the risk
This risk spans every major security domain. Today, an attacker can download a signed operating system image and extract the public keys used to verify it. While benign for now, this changes in a quantum future. Once quantum computers can defeat today’s code‑signing cryptography, an attacker could compromise a vendor’s private signing keys and use them to insert backdoors or malware into bootloaders and operating systems that still appear fully trusted.
The same risk applies to encrypted network communications. Encrypted data over Internet Protocol Security (IPsec) or Media Access Control Security (MACsec) can be collected and stored today without being readable. When quantum computers become available, the public-key cryptography used to establish session keys can be broken, allowing previously captured data to be decrypted long after it was transmitted.
Why a full-stack architectural approach is essential
Addressing this risk is not confined to any single security control, protocol, or layer. It requires a full-stack architectural approach that applies quantum‑safe cryptography consistently across device integrity and network communications.
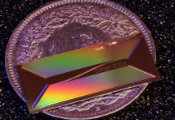
The Cisco full-stack PQC architecture is built around this principle: protect what runs (device integrity) and what flows (data in transit) with quantum-safe cryptography applied end to end. Protection begins before the operating system even loads, with Cisco Secure Boot establishing a quantum‑safe chain of trust for Cisco C9000 Smart Switches from the moment they power on. By cryptographically validating each stage of the boot process with quantum-resistant algorithms, it ensures that only verified software runs, creating a solid and secure foundation for network operations.
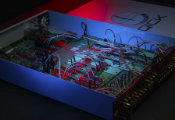
That same architectural principle applies to how data moves across the network. From IPsec tunnels connecting branches to MACsec securing the campus, Cisco integrates quantum‑resistant key exchange directly into critical network protocols. The result is consistent, quantum‑safe protection across the full technology stack without requiring disruptive changes to network design or operations.
For large enterprise networks—where real-time collaboration, AI-driven automation, and high-value data flows are the norm—this “security fused into the network” model is essential for digital resilience at scale.
Engineering for resilience starts now
For IT leaders managing large enterprise infrastructures, the safest time to build quantum resistance into the stack is during ongoing upgrade cycles—not after the threat becomes urgent.
Start by auditing current device authentication and encryption workflows to pinpoint dependencies on RSA- and ECC-based algorithms. Prioritize upgrades to platforms supporting full-stack PQC, ensuring both device integrity and network traffic are secured against quantum threats.
With quantum-resilient networking as a core capability, enterprises can confidently deploy AI-driven applications, maintain uninterrupted operations, and mitigate risks from rapidly advancing cyberthreats.
Full-stack PQC is the new reality for enterprise security
Full-stack PQC is not a speculative concept; it’s physics. The transition to Cisco IOS XE 26 represents a maturing of the security landscape in which Cisco stop assuming their encryption is unbreakable and start engineering for a world where it isn’t.
Whether you are defending against HNDL attacks today or preparing for compliance with the NSA’s CNSA 2.0 timeline, the path forward is clear. The quantum clock is ticking, and the time to act is now.